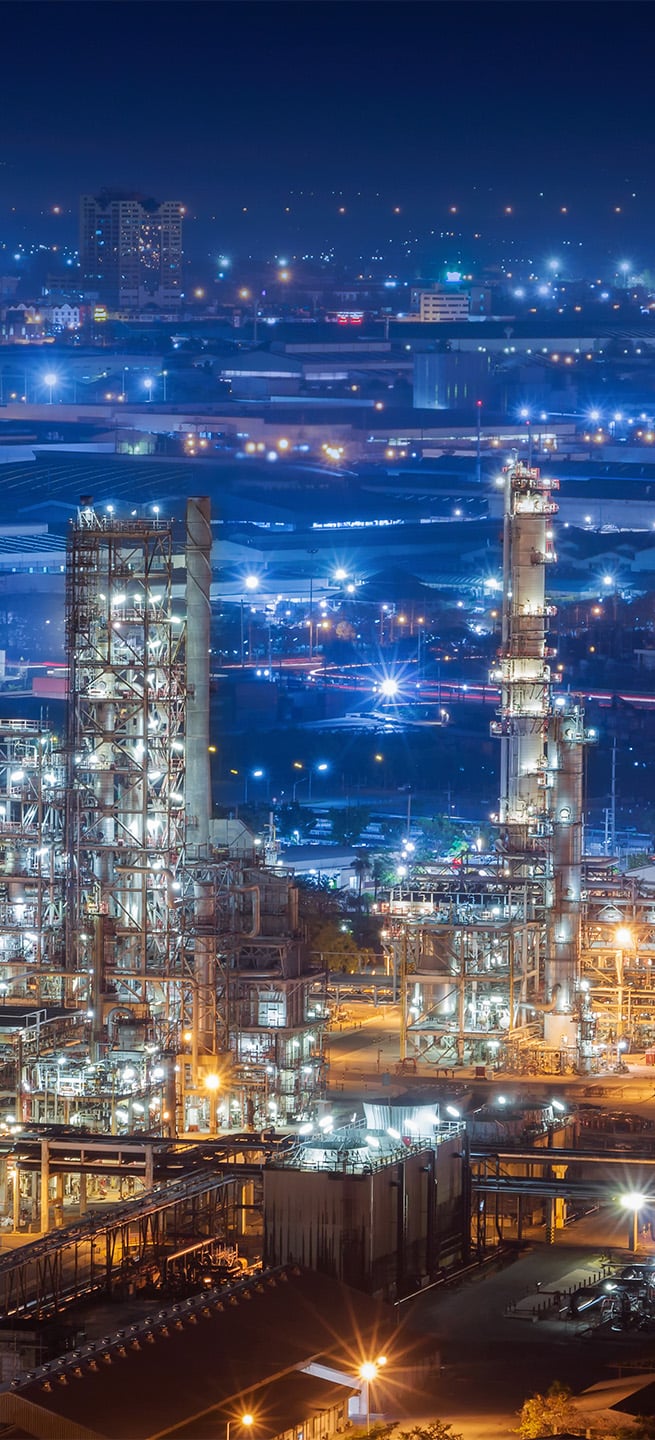
Operational Technology Cybersecurity is a Global Imperative
The ISA Global Cybersecurity Alliance (ISAGCA) is a global consortium working to secure critical infrastructure.

What is OT Cybersecurity?
As smart manufacturing technologies are increasingly implemented and begin to mature, new and increased cybersecurity challenges have emerged beyond device-level IT risks.
Termed “operational technology” or OT cybersecurity, this field refers to the security and safety of industrial environments, and it is of critical importance when it comes to securing infrastructure, supply chains, and more.
ISAGCA is Your Voice in OT Cybersecurity
Created by the International Society of Automation (ISA), the ISA Global Cybersecurity Alliance (ISAGCA) is a collaborative forum to advance OT cybersecurity awareness, education, readiness, standardization, and knowledge sharing.
50+ Members
The ISA Global Cybersecurity Alliance is made up of 50+ member companies, representing more than $1.5 trillion in aggregate revenue across more than 2,400 combined worldwide locations.
31 Industries
Automation and cybersecurity provider members serve 31 different industries, underscoring the broad applicability of the ISA/IEC 62443 series of standards upon which our efforts are based.
Addressing Threats
Governments around the world are becoming more concerned about the impact of cybersecurity vulnerabilities, especially when it comes to critical infrastructure applications. We can't approach this unilaterally—we can only approach it together.
The Foundation of Our Work is ISA/IEC 62443
The International Society of Automation (ISA) developed the world’s only consensus-based cybersecurity standards for automation and control system applications.
- 1
The ISA/IEC 62443 series of standards have been endorsed by the United Nations and codify extensive operational technology and IoT cybersecurity subject matter expertise.
- 2The standards define requirements and procedures for implementing electronically secure automation and industrial control systems and security practices and assessing electronic security performance.
- 3The series approaches the cybersecurity challenge in a holistic way, bridging the gap between operations and information technology; and between process safety and cybersecurity. Stakeholders leverage ISA/IEC 62443 throughout the lifecycle, from product designers and integrators to service providers and asset owners.
How We Do Our Work
ISAGCA was created to address cybersecurity threats and vulnerabilities that are clear and present dangers to our facilities, our processes, and the safety of our communities.
Standards
ISAGCA raises awareness of the ISA/IEC 62443 series of standards, the world’s leading consensus standards for OT cybersecurity.
Adoption
ISAGCA works with a broad spectrum of stakeholders to encourage reliance upon ISA/IEC 62443 in laws, regulations, and other standards across industry sectors.
Compliance
Globally recognized standards are important, but conformity assessment is the other side of the coin. Reduce risk and increase peace of mind with certification.
Incident Response
An ISAGCA effort – ICS4ICS, the Incident Command System for Industrial Control Systems – helps operating sites respond to and recover from attacks.
Featured In


















EDUCATION AND LEARNING
ISA/IEC Technical Resources
ISA offers a number of free resources to increase awareness of the importance of OT cybersecurity, and how to apply ISA/IEC 62443 to various environments and scenarios.
Elevating OT Cybersecurity from an Art, to a Science, to an Engineering Discipline
We must work together to change the culture among engineers to recognize cybersecurity as a fundamental workplace tenet alongside functionality, efficiency, and safety.
ISAGCA is your forum to make this change a reality.