A version of this blog originally appeared on Cisco
When you think about cybersecurity, I bet you think about protection from malware–pieces of software that can infiltrate industrial resources and steal data or disrupt operations. Such security requires sophisticated firewalls, deep packet inspection, intrusion detection and prevention, and a robust network that can segment operations and limit any malware's spread.
That's great, but you might be ignoring vulnerabilities that can arise from deficiencies in the underlying hardware. If you are, you would be making a grave error. If the hardware is not reliable, any security measures you take on the network and resources that run on that hardware can’t be relied upon. Securing the hardware should be considered fundamental to securing operations.
The Hardware Can Be a Source of Vulnerabilities
Compromised hardware may have counterfeit products that have a higher risk of downtime, backdoors, logic bombs, built-in malware and spyware, inferior components, and a greater potential for denial-of-service attacks. Such hardware could be ticking time bombs.
Very recently, a CEO of dozens of companies was charged in a scheme to traffic an estimated $1 billion in fraudulent and counterfeit Cisco networking equipment. The chargesheet reads—among other allegations—that the counterfeiters added, “unauthorized, low-quality, or unreliable components–including components to circumvent technological measures added by Cisco to the software to check for software license compliance and to authenticate the hardware.”
As a leading provider of enterprise and industrial networking and security products, we at Cisco are committed to ensuring that our networking equipment is hardened and provides that secure stable base that you can rely on to build your mission critical operations.
ISA/IEC 62443: Cybersecurity for Industrial Operations
The industrial automation and control systems (IACS) industry has developed a comprehensive framework that lays out the best practices for robust industrial cybersecurity for both vendors and users. This framework considers measures against both software and hardware-based attacks and was initially developed by the International Society of Automation (ISA) as the ISA99 standards. The International Electrotechnical Committee (IEC) subsequently built on that work and produced the IEC 62443 set of standards. As shown in the diagram, the standard consists of four building blocks–each of which is a standard in itself.
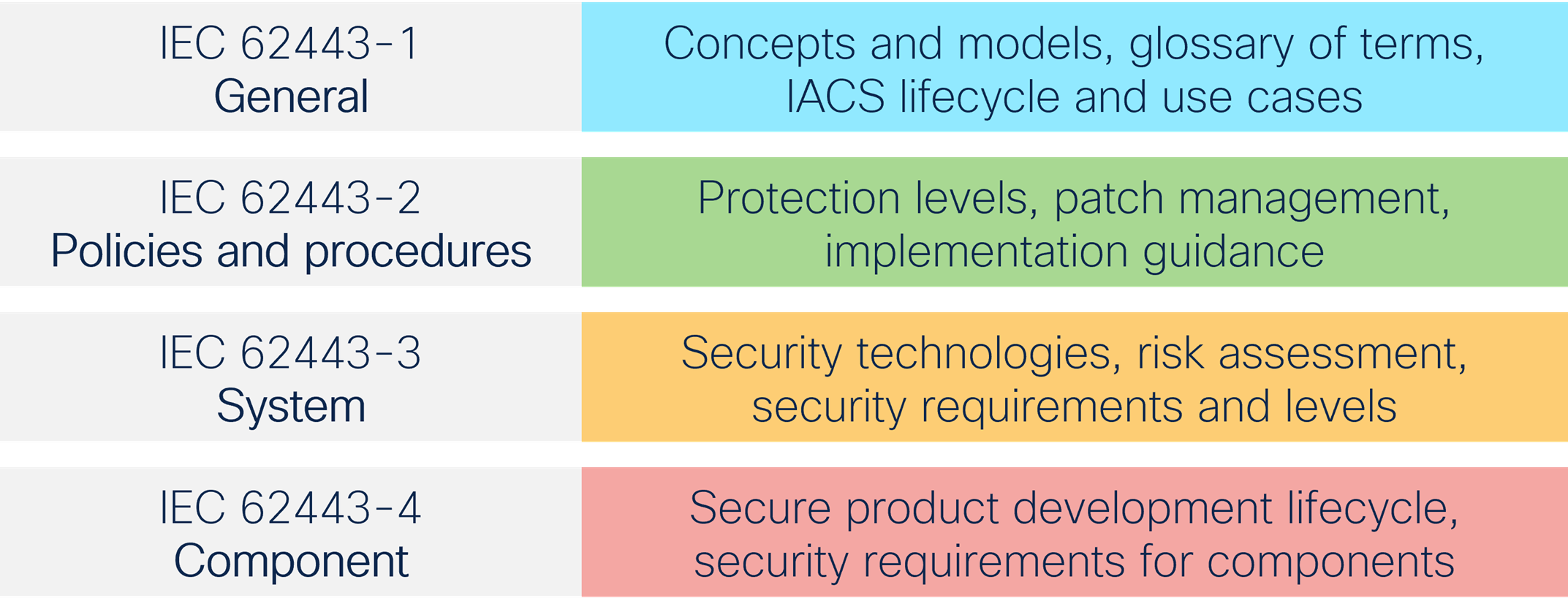 Figure 1: IEC 62443 set of standards
Figure 1: IEC 62443 set of standards
We have previously written about the various parts of this wide-ranging standard (see What is ISA/IEC 62443 and Cisco one of first networking companies to receive two IEC 62443 certifications for industrial switches). In this blog, I will describe how security is built into the complete lifecycle of our entire industrial networking equipment portfolio that complies with the IEC 62443-4 part of the standard. IEC 62443-4 consists of two parts, as described below.
ISA/IEC 62443-4-1: Secure Product Development Lifecycle Requirements
The first part, IEC 62443-4-1, describes how the underlying products must be developed so that they meet required security standards considerations. IEC 62443-4-1 describes requirements for the secure development of products used to assemble IACS as well as maturity levels to set benchmarks for compliance. These requisites include requirement, management, design, coding guidelines, implementation, verification and validation, defect management, patch management, and product end-of-life. All of these are essential to the security capabilities of a component and the underlying secure-by-design approach of the IACS solution. The overall focus is on continuous improvement in product development and release.
Cisco software and hardware products are developed according to the Cisco Secure Development Lifecycle (CSDL), which enforces a secure-by-design philosophy from product planning through end-of-life. CSDL comprehensively addresses security from planning, operating, and monitoring stages. 
- Plan: Extensive threat modeling and assessments help us build security and privacy into our technology right from the start rather than “bolt on” afterwards.
- Develop: We use secure coding standards, threat-resistant code, and follow security best practices. Extensive code reviews prevent defects and minimize security weaknesses.
- Validate: Our testing regimen incorporates industry-leading protocol tests, open-source and commercial tools, and sophisticated application test methods for vulnerability and penetration testing.
- Launch: Our strict pre-launch criteria tests readiness and prepares the product for customer use.
- Operate: Our security preparedness does not stop at product launch. Cisco’s Product Security Incident Response Team (PSIRT) monitors security events, coordinates fixes, and sends notification to customers.
- Monitor: Cisco’s Talos threat intelligence group research potential threats and shares actionable information with the broader security community to build better defenses.
ISA/IEC 62443 4-2: Technical Security Requirements for IACS Components
IEC 62443-4-2 contains requirements for components necessary to provide the required security base for 62443-3 and higher levels. In this regard, the standard specifies security capabilities that enable hardware equipment to be integrated into a secure IACS deployment. Part 4-2 contains requirements for four types of components: Software application, embedded device, host device, and network device. In essence, a secure IACS solution needs to be built based on secure components. The upper-layer recommendations, such as IEC 62443-3-3, assume that secure components will be deployed to meet the corresponding requirements that address the current and future vulnerability and threat landscape.
Several Cisco products have already achieved IEC 62443-4-2 certification. In combination with a 62443-certified development process (CSDL), Cisco offers trustworthy communication products which are essential for IACS deployment in critical infrastructures.
Cisco Trustworthy Technologies
 In addition to benefiting from secure development methodologies, Cisco Industrial Ethernet Switches contain several embedded security features that provide additional layers of protection. These include the Trust Anchor Module that authenticates hardware for immutable device identity and secure storage, among others. These switches also feature Secure Boot that ensures that only authentic and unmodified software boots up on them, Signed Images that protect against insertion of counterfeit and tampered software, and Runtime Defenses that protect running devices from attacks that change product software execution.
In addition to benefiting from secure development methodologies, Cisco Industrial Ethernet Switches contain several embedded security features that provide additional layers of protection. These include the Trust Anchor Module that authenticates hardware for immutable device identity and secure storage, among others. These switches also feature Secure Boot that ensures that only authentic and unmodified software boots up on them, Signed Images that protect against insertion of counterfeit and tampered software, and Runtime Defenses that protect running devices from attacks that change product software execution.
Our Commitment Doesn’t End Here
Not only does Cisco build products that comply with existing industrial networking and security standards (such as IEC 61850 for utilities), but we also help move them forward with active participation and leadership in IEC, ISA, IEEE, and other standard-setting bodies.
For further reading, please refer to the following: The Cisco Trust Center, Cisco Trustworthy Solutions




