Introduction
Many organizations (especially very large ones) have established policies and procedures governing the IT security in their office environment; many of these are based on ISO/IEC 27001/2 [27001] [27002]. Some have attempted to address their operational technology (OT) infrastructure under the same management system, and have leveraged many IT/OT commonalities. Although it would be ideal to always select common controls and implementations for both IT and OT, organizations have been confronted with challenges in doing so, such as OT operator screen locking creating unsafe conditions, antivirus products incompatible with OT equipment, patching practices disrupting production schedules, or network traffic from routine backups blocking safety control messages. The ISA/IEC 62443 series explicitly addresses issues such as these; this helps an organization to maintain conformance with ISO/IEC 27001 through common approaches wherever feasible, while highlighting differences in IT vs. OT approach where needed.
This document offers guidance for organizations familiar with ISO/IEC 27001 and interested in protecting the OT infrastructure of their operating facilities based on the ISA/IEC 62443 series. It describes the relationship between the ISA/IEC 62443 series and ISO/IEC 27001/2 and how both standards may be effectively used within one organization to protect both IT and OT.
62443 does not require the use of an underlying Information Security Management System (ISMS), However it requires that, if the organization has an established ISMS, the security program in the OT environment should be coordinated with it. In this document we are considering the use case of an existing ISMS based on ISO/IEC 27001/2.
Other information security standards similar in scope to 27001 might be used effectively together with 62443 under an approach similar to that described here. Evaluation of such approaches is outside the scope of this paper. However, users of such standards are encouraged to explore that possibility.
Background
Scope of ISO/IEC 27001/2
The standard ISO/IEC 27001 provides requirements for establishing, implementing, maintaining, and continually improving an ISMS as well as a list of commonly accepted controls to be used as a reference for establishing security requirements (ISO/IEC 27000, the glossary and introduction to the 27000 series, defines the term control as “measure that is modifying risk”). In addition, ISO/IEC 27002 provides further detailed guidance for organizations implementing these information security controls. It is designed for organizations to use as a reference for selecting controls within the process of implementing an ISO/IEC 27001 conformant ISMS.
IT and OT
“IT” is the common term for the entire spectrum of technologies for information processing, including software, hardware, communications technologies, and related services [Gartner-ITG]. “Operational technology” or “OT” is hardware and software that detects or causes a physical change, through the direct monitoring and/or control of industrial equipment, assets, processes and events [Gartner-ITG]. Increasingly, IT products and systems are used in OT infrastructures, and recently, the advent of IoT (Internet of Things) and Industrial Internet of Things has further blurred the IT/OT distinction. However, the main difference is that OT environments in general must comply with strict integrity, availability, and performance constraints due to the fact that operation outside of the constraints may impact health, safety, or the environment.
Scope of the ISA/IEC 62443 series
The scope of the ISA/IEC 62443 series of standards is the security of “Industrial Automation and Control Systems (IACS)” used in OT infrastructures. This includes control systems used in manufacturing and processing plants and facilities, geographically dispersed operations such as utilities (i.e., electricity, gas, and water), pipelines and petroleum production and distribution facilities. The ISA/IEC 62443 series has also gained acceptance outside of its original scope, for example in building automation, medical systems, and in other industries and applications such as transportation networks, that use automated or remotely controlled or monitored assets.
Figure 1 gives an overview of the scope of some core documents of the ISA/IEC 62443 series. Part 62443-2-1 [62443-2-1] is targeted at organizations that are responsible for IACS facilities, which includes owners and operators (termed “asset owners” in the series) and provides requirements for asset owner IACS security programs.
In addition, the ISA/IEC 62443 series provides conformance requirements for all entities supporting asset owners in the implementation of technical and procedural security measures for the protection of operating facilities from cyber threats. Part 62443-2-4 [62443-2-4] provides security requirements for integration and maintenance service providers supporting asset owners in the development and operation of OT specific technical solutions. Parts 62443-3-3 [62443-3-3] and 62443-4-2 [62443-4-2] define requirements for security capabilities of systems and components, respectively. Part 62443-4-1 [62443-4-1] includes lifecycle requirements for product suppliers for the development and support of products with adequate security capabilities. In addition, the ISA/IEC 62443 series includes guidance documents for specific issues like patch management and risk-based system partitioning in zones and conduits.
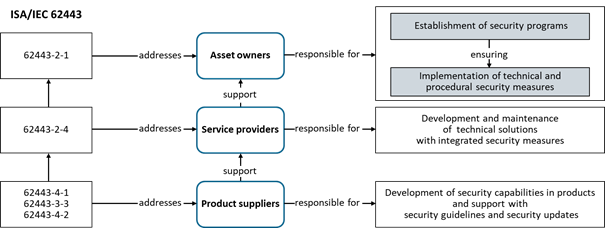
Figure 1. ISA/IEC 62443 addresses all entities involved in the protection of operating facilities
Note: The present document refers to the most recent version of part 62443-2-1, which is not finally approved as an International Standard and may be subject to changes. It is not expected that these changes will impact the recommendations of this paper.




