Optimizing for Increased Adoption and Application
The ISA Global Cybersecurity Alliance (ISAGCA) was formed in part to help increase awareness and adoption of the ISA/IEC 62443 standards, the world's only consensus-based series of automation cybersecurity standards. This blog series will share insights into the creation and evolution of the standards.
Awareness of the ISA/IEC 62443 standards for industrial automation and control systems security has increased dramatically in recent years. Although these standards have existed for well over a decade, it has been the recent release of standards dealing with topics such as risk assessment, secure development lifecycles, and detailed component level security that has led to increased interest from a variety of industry sectors. Yet acceptance and adoption of these standards is still not where it should be.
Part of the reason for this is the amount of information included in the standards and their perceived complexity. In particular, asset owners find it daunting to fully understand the standards and are typically faced with the very real challenge of deciding how to begin to address what can be seen as a very complex and challenging topic. Awareness of what is available is certainly a good start, but it must be followed by understanding as a prerequisite to acceptance and adoption.
The ISA99 committee is primarily responsible for much of the organization and content of the series, working in collaboration with IEC Technical Committee 65 Work Group 10 (TC65 WG10). It is important to remember that normative standards are intended to serve as references, supplemented by more direct and focused guidelines and supporting materials.
In planning the organization of content in the series, it is important to recognize that there are multiple perspectives or dimensions that must be considered. While some readers may be most interested in understanding the requirements for (and expectations of) various roles, others may be more focused on technology selection. Another perspective considers the stages of the lifecycle from design and implementation to operation and support. Finally, an automation system can be viewed as a series of levels—from individual components or devices to systems and more complex systems of systems. It is difficult to accommodate all these perspectives in a single description of the structure of the series.
The series description that is most commonly used is show in the following figure.
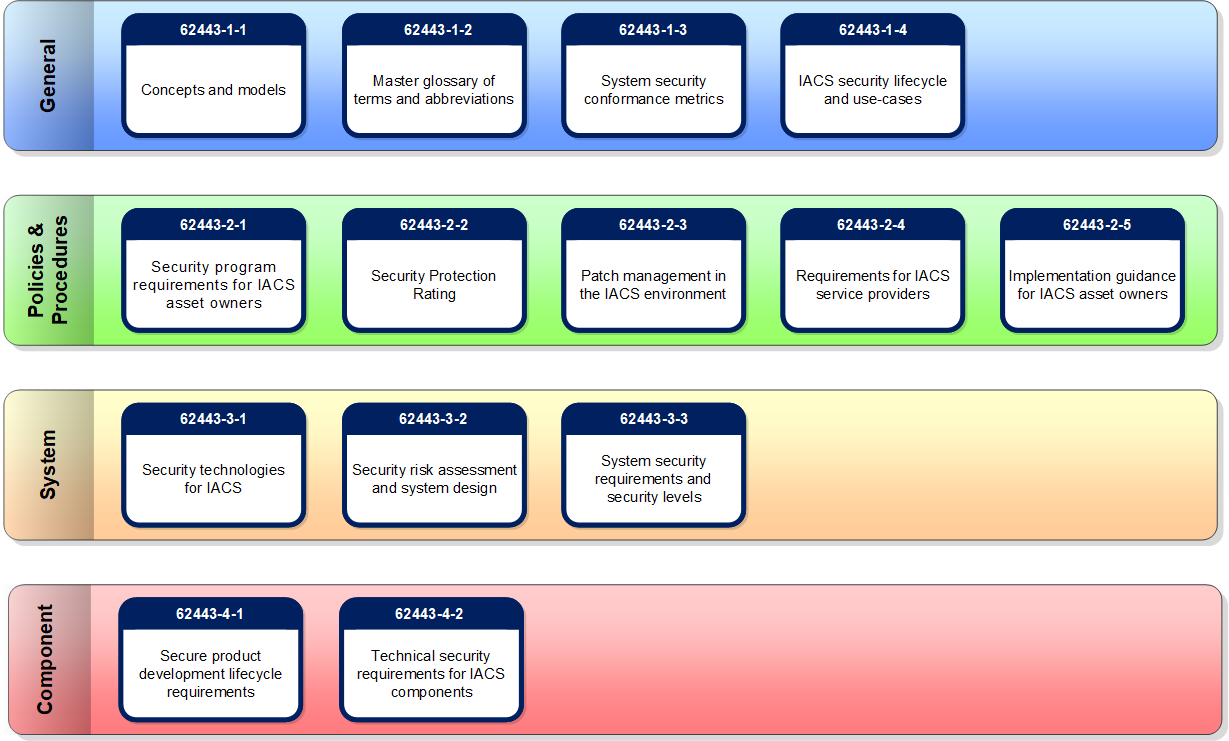 Diagram of the ISA/IEC 62443 Series of standards
Diagram of the ISA/IEC 62443 Series of standards
This view has been developed by the committee over a period of several years, with new documents added as they were identified. It represents a combination of system level and role, although neither perspective is fully addressed. Each document is associated to one of four groups:
1. General
This group includes documents that address topics that are common to the entire series.
- 62443-1-1 introduces the concepts and models used throughout the series. The intended audience includes anyone wishing to become familiar with the fundamental concepts that form the basis for the series.
- 62443-1-2 is a master glossary of terms and abbreviations used throughout the series.
- 62443-1-3 describes a series of quantitative metrics derived from the foundational requirements, system requirements, and other guidance material in the standards.
- 62443-1-4 provides a more detailed description of the underlying lifecycle for IACS security, as well as several use cases that illustrate various applications.
2. Policies and Procedures
Documents in this group focus on the policies and procedures associated with IACS security.
- 62443-2-1 describes what is required to define and implement an effective IACS cybersecurity management system. The intended audience includes end users and asset owners who have responsibility for the design and implementation of such a program.
- 62443-2-2 provides a methodology for evaluating the level of protection provided by an operational IACS against cybersecurity threats and how to apply what is required by 62443-2-1.
- 62443-2-3 provides guidance on patch management for IACS. The intended audience includes anyone who has responsibility for the design and implementation of a patch management discipline.
- 62443-2-4 specifies requirements for suppliers of IACS systems and related components. The principal audience include suppliers of control systems solutions. This standard was developed by IEC TC65 WG10.
- 62443-2-5 provides guidance on what is required to operate an effective IACS cybersecurity management system. The intended audience includes end users and asset owners who have responsibility for the operation of such a program.
3. System Requirements
The documents in the third group address requirements at the system level.
- 62443-3-1 describes the application of various security technologies to an IACS environment. The intended audience includes anyone who wishes to learn more about the applicability of specific technologies in a control systems environment.
- 62443-3-2 addresses security risk assessment and system design for IACS. This standard is primarily directed at asset owners or end users.
- 62443-3-3 provides the foundations for assessing the security levels provided by an automation system. The principal audience include suppliers of control systems, system integrators, and asset owners.
4. Component Requirements
The fourth and final group includes documents that provide information about the more specific and detailed requirements associated with the development of IACS products.
- 62443-4-1 describes the derived requirements that are applicable to the development of products. The principal audience include suppliers of control systems products and of components included in control systems solutions.
- 62443-4-2 contains sets of derived requirements that provide a detailed mapping of the system requirements to subsystems and components of the system under consideration. The principal audience include suppliers of components embedded in control systems solutions.
ISA99 committee members are now reviewing this organization to identify potential improvements that might contribute to increased acceptance and adoption. This activity is part of a larger and more broadly focused project to assess the consistency of the standards and make recommendations for improvements. Any such recommendations must first be approved by committee leaders and then implemented in a manner that eases transition. Continuity from one structure to another is critical for those who have already adopted or applied one or more standards. For example, existing document numbers must be retained through the first phase of transition. They may be modified in later phases, but only via a well-defined change management process.
In summary, the ISA99 committee is very aware of the importance of addressing misconceptions and possible impediments to the acceptance and adoption of the 62443 standards. With much of the most important content of the series completed, now is the time to “step back,” take a fresh look at this material, and determine whether the structure and organization can be improved to meet this need. Any and all such changes will be made using the same processes and transparency that were used in creating the standards. This will include circulation of information for review and comment and submitting any changes to both the voting members of ISA99 and IEC TC65 WG10 for approval.
ISAGCA has created a quick start guide to the ISA/IEC 62443 standards. If you're interested in learning more, please request your free copy of the guide.




